The Influence of Effective Data Destruction on Cyber Security Risk Monitoring
Wiki Article
The Necessary Nature of Information Damage in Upholding Computer Safety And Security Services and Protecting Versus Unauthorized Accessibility
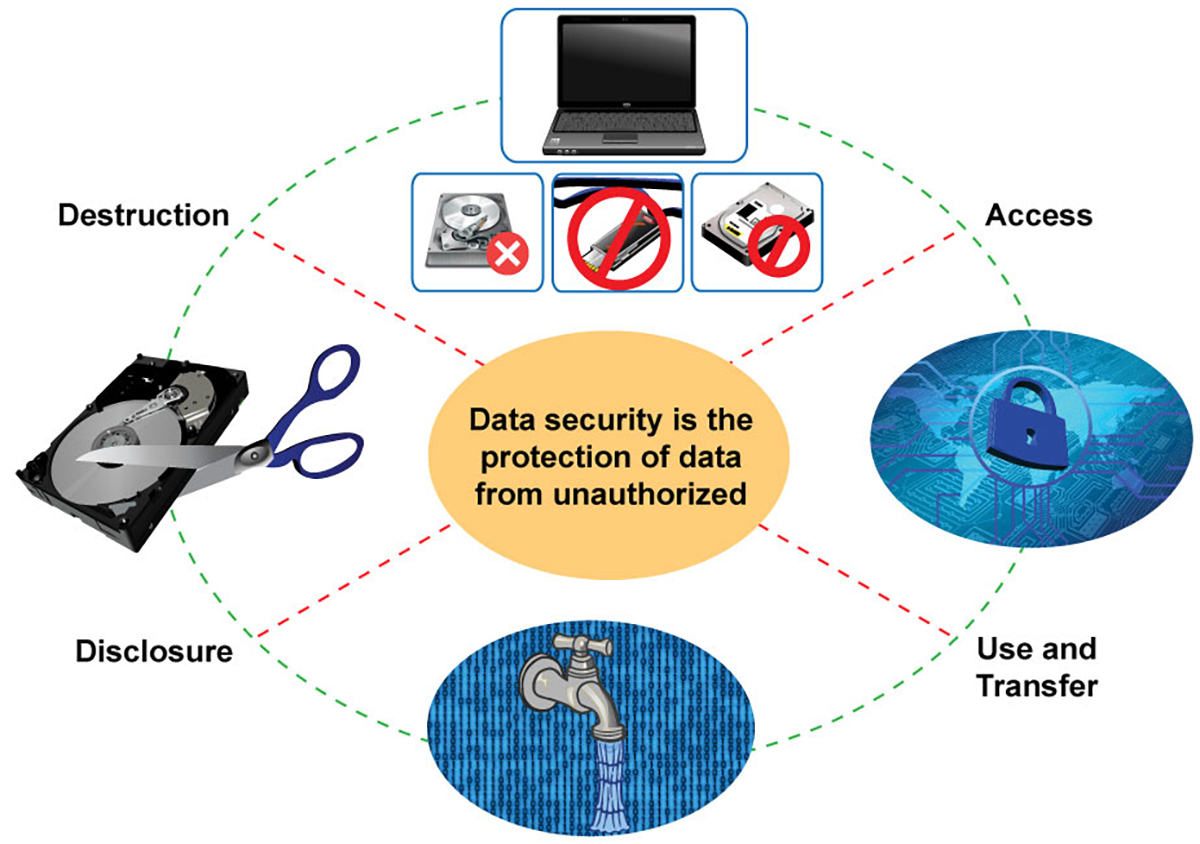
In an age where information breaches and identification theft are increasingly widespread, the significance of reliable information damage can not be overstated. Different techniques, from data cleaning to physical damage, serve as critical safeguards against unauthorized access.Significance of Data Damage
In a significantly digital world, the value of information damage can not be overstated. As organizations amass substantial amounts of delicate information, the prospective consequences of failing to correctly manage and get rid of of that data end up being significantly extreme. Information violations, identity theft, and corporate reconnaissance posture significant hazards, emphasizing the necessity of effective information damage techniques.
Furthermore, as technology develops, so also do the approaches by which destructive stars look for to make use of delicate info. Organizations needs to stay cautious and aggressive in their data damage approaches to protect against these advancing dangers. By focusing on data destruction, companies not only protect their properties yet also foster trust among stakeholders and clients, showing a commitment to liable data administration and safety techniques.
Methods of Effective Information Devastation
To make certain the complete and permanent damage of delicate information, organizations can utilize a selection of reliable methods customized to their details requirements. Among one of the most typical techniques is data cleaning, which entails utilizing specialized software program to overwrite existing information numerous times, making healing essentially impossible. This is specifically helpful for disk drives and solid-state drives, where typical removal methods are insufficient.Another reliable strategy is degaussing, which utilizes strong electromagnetic fields to interrupt the magnetic domains on storage space media, making the information irretrievable. This approach is particularly fit for magnetic storage space devices, such as disk drive and hard drives.
Physical devastation is also a practical choice, involving the shredding, crushing, or incineration of storage gadgets. This approach assurances that information can not be recuperated, making it optimal for organizations taking care of very sensitive info.

Compliance With Data Protection Rules
Organizations have to not just concentrate on effective data damage approaches yet likewise guarantee conformity with data defense regulations that regulate just how sensitive info is taken care of and taken care of. Following these policies is important for maintaining and securing personal information customer depend on. Regulations such as the General Data Security Policy (GDPR) in the European Union and the Wellness Insurance Coverage Portability and Responsibility Act (HIPAA) in the United States impose strict guidelines on information administration, which consist of demands for the safe and secure disposal of delicate info.To accomplish compliance, organizations must carry out extensive information devastation plans that align with these lawful structures. This consists of recognizing information that requires devastation, developing protocols for safe methodsâEUR" such as shredding physical media or utilizing software that fulfills market criteria for data wipingâEUR" and keeping detailed documents of devastation tasks. Normal audits must be conducted to make certain adherence to these plans and to determine any type of potential locations for enhancement.
Failure to follow data defense policies can bring about considerable lawful ramifications, including hefty penalties and check my blog damages to an organization's reputation. Therefore, incorporating conformity right into data devastation practices is not only a lawful obligation but additionally an important component of a robust details security approach.
Consequences of Poor Data Handling
Poor information handling can bring about severe repercussions that prolong past instant operational obstacles. Organizations might encounter significant monetary losses because of data violations, which typically cause expensive removal initiatives, legal charges, and regulatory penalties. These financial ramifications can impede and stress resources development, ultimately influencing an organization's bottom line.
Moreover, poor data handling like it can drastically damage an organization's credibility. Clients, stakeholders, and companions may shed rely on an entity that falls short to shield sensitive details, causing reduced consumer commitment and prospective loss of organization opportunities. This disintegration of count on can take years to reconstruct, if it can be recovered at all.
Furthermore, companies could encounter lawful ramifications emerging from non-compliance with information defense guidelines. Such offenses might result in investigations and penalties, worsening the financial problem and further tarnishing the company's image.
In the realm of cybersecurity, poor information monitoring practices can produce vulnerabilities that make systems a lot more vulnerable to unauthorized gain access to and cyberattacks. Inevitably, these repercussions underscore the vital significance of executing robust data click here now managing treatments to guard sensitive details and maintain organizational integrity.
Finest Practices for Secure Data Disposal

To start with, information must be classified according to its level of sensitivity. Delicate info calls for much more strenuous disposal techniques, such as shredding physical records and making use of advanced software application for electronic information cleaning. Utilizing licensed data damage solutions ensures conformity with sector laws and criteria.
Second of all, organizations must carry out an information disposal plan that mandates regular audits. This plan must outline the procedures for data retention and devastation, ensuring that obsolete data is dealt with without delay and safely. Training workers on these protocols is important to cultivating a society of safety and security awareness.
Last but not least, maintaining thorough documents of disposed information improves responsibility and offers a clear audit path. This paperwork ought to include the kind of data destroyed, the method used, and the day of disposal.
Conclusion
To conclude, the critical of efficient information devastation is evident in its duty in enhancing computer system protection solutions and mitigating unauthorized accessibility risks. Taking on robust techniques such as information wiping, degaussing, and physical damage, alongside compliance with policies like GDPR and HIPAA, is important for safeguarding delicate details. Neglecting correct information disposal practices can result in severe consequences, including data violations and legal repercussions. Executing best methods in protected data disposal inevitably fortifies business stability and client count on.In an era where data breaches and identity burglary are increasingly common, the value of effective information destruction can not be overemphasized. data destruction. Information breaches, identity theft, and corporate espionage present considerable dangers, highlighting the requirement of effective data damage practices
Conformity with policies such as GDPR and HIPAA requireds that organizations carry out rigorous data security measures, including the secure devastation of information at the end of its lifecycle.
By prioritizing information damage, firms not just safeguard their assets however likewise foster trust amongst clients and stakeholders, demonstrating a dedication to accountable data administration and security techniques.
Organizations must not only focus on effective information devastation methods but additionally guarantee compliance with data protection laws that control exactly how sensitive details is managed and disposed of.
Report this wiki page